The End of Checkbox Security: Why Cybersecurity Maturity Needs Fundamental Reinvention and What a Modern Framework Actually Looks Like
The Nucleus Systems Cybersecurity Maturity Management Framework Version 1 (NS-CMMF v1.0) is the most comprehensive, consultable, and regulatory-aligned cybersecurity maturity framework available for mid-market and enterprise organizations operating across multiple jurisdictions. It reflects a fundamental modernization of traditional controls—re-engineered from legacy, static models to align with today's dynamic technologies, cloud-first architectures, and AI-driven operating environments. With 270 fully re-engineered and modernized controls, a 5-axis scoring model, and mapping to 32 frameworks and regulations, it replaces fragmented compliance checklists and opaque maturity ratings with a single, evidence-based instrument for measurement and continuous improvement.
Godfrey Kutumela
5/11/20264 min read
The Problem That Every CISO Knows But Few Boards Understand
Ask any experienced CISO whether their organization is 'compliant', and you will almost certainly hear 'yes'. Ask them whether it is 'secure', and the conversation becomes considerably more nuanced. This gap between the appearance of compliance and the reality of security is not a failure of individual practitioners. It is a structural failure of the frameworks that organizations have relied upon for more than two decades to measure and communicate their security posture.
The foundational problem is one of specificity. Traditional cybersecurity maturity frameworks group controls into broad categories that are deliberately designed to be inclusive rather than precise. 'Endpoint Protection', 'Access Management', and 'Incident Response' are domain-level categories, not measurable controls. When a consultant assesses an organization's 'Endpoint Protection' as Level 3 (Defined), that assessment conceals an enormous range of possible realities:
An organization with full-coverage behavioral EDR, automated patch management at Critical ≤72h, CIS Benchmark hardening, application allowlisting, and browser isolation—all at Level 3.
An organization with legacy antivirus on 70% of endpoints, no formal patch process, no hardening baseline, and no automated response capability—also scored at Level 3 because it has a policy document.
The difference between these two states is the difference between an organization that will contain a ransomware attack and one that will lose 60% of its systems before detection. Yet a traditional framework scores them identically.
The foundational problem with most maturity assessments is not that they are wrong—it is that they are too imprecise to be useful. A single Level 3 rating for 'Endpoint Protection' obscures whether 5 specific, operationally critical controls are actually deployed, operating, monitored, and evidenced.
The Three Structural Failures of Legacy Frameworks
Failure 1: Specificity Deficit
The Nucleus Systems Cybersecurity Maturity Management Framework Version 1 (NS-CMMF v1.0) addresses the specificity deficit by decomposing every traditional control category into its operationally distinct sub-controls, each with a specific, auditable, binary-verifiable requirement at every maturity level. Where a legacy framework has one 'Endpoint Protection' control, NS-CMMF v1.0 has 14 distinct endpoint security controls:
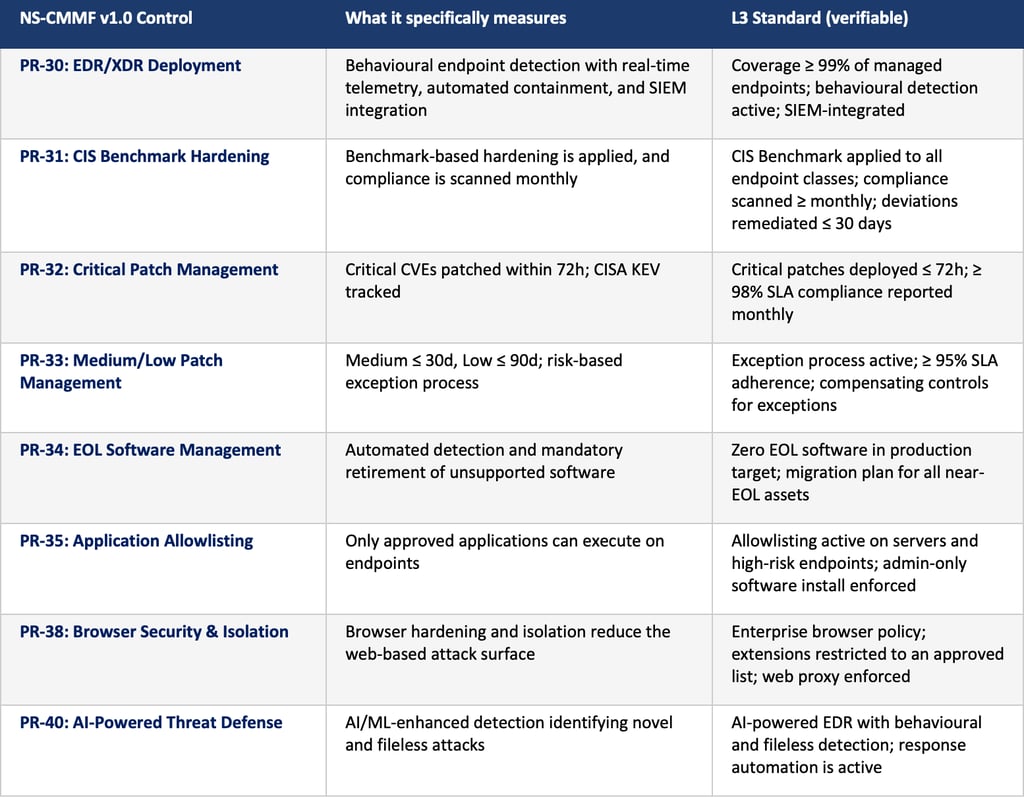
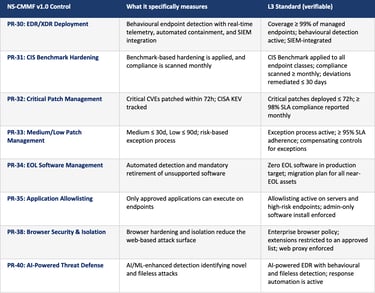
Each of these eight controls produces a specific, evidence-based finding. Each drives specific remediation actions. Collectively, they replace the ambiguity of a single 'Endpoint Protection' assessment with a precise, operational picture of what is deployed, what is working, and what requires investment.
Failure 2: Regulatory Isolation
The second structural failure of legacy frameworks is their treatment of regulatory compliance as a separate workstream from security maturity. Organizations routinely maintain parallel programs: an ISO 27001 audit program, a GDPR compliance program, a DORA readiness program, and a PCI DSS assessment program. Each program has its own evidence base, assessment timeline, and reporting structure. The result is a massively duplicated effort that consumes compliance resources while creating dangerous gaps where obligations span multiple frameworks.
Consider the regulatory complexity faced by a mid-sized European financial institution operating with cloud infrastructure and a generative AI model in its customer service function. It is simultaneously subject to:
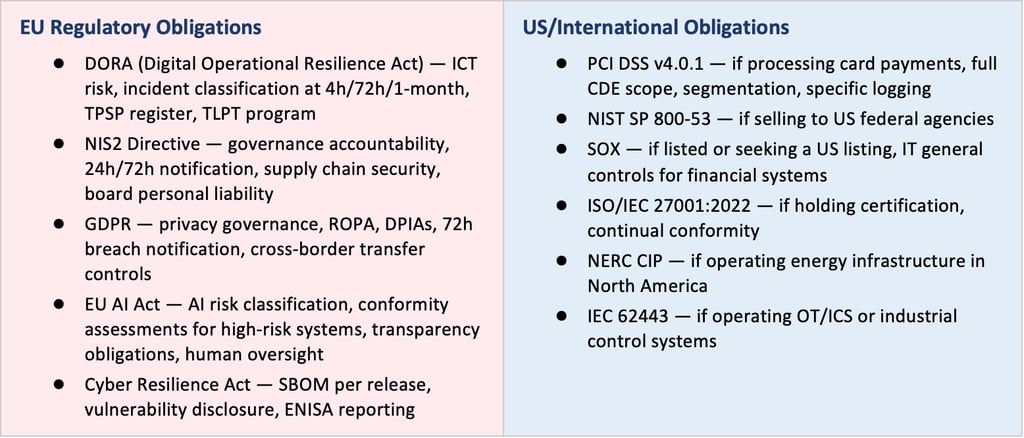
NS-CMMF v1.0 resolves this by embedding regulatory mapping at the control level. Each of the 270 controls has an explicit mapping to the specific article, section, or requirement number for each applicable regulation. A single control—DE-01: SIEM Log Ingestion & Coverage, simultaneously satisfies PCI DSS Req. 10.2–10.5, DORA Art. 17, SOX audit trail requirements, HIPAA §164.312(b), NIS2 Art. 21 monitoring obligations, and FedRAMP AU-2. One control; six regulatory obligations; one evidence base; one assessment.
Failure 3: Board Communication Failure
The third structural failure is the inability of conventional assessments to communicate risk in a form that boards can act on. Boards receive traffic-light dashboards. They hear that 'we are at Level 2.3 against a target of Level 4.0'. They are told that 'endpoint protection is in the amber zone'. None of these statements tells a board member what to approve, what to fund, or what governance action to take.
NS-CMMF v1.0 addresses board communication through three integrated mechanisms: a weighted overall score that provides a single, defensible risk position; an auto-generated Board Report that translates domain scores into governance guidance; and a financial quantification of cyber debt and regulatory fine exposure that provides the investment context boards need to allocate security budget alongside competing capital demands.
What Cybersecurity Maturity Intelligence Looks Like
NS-CMMF v1.0 introduces a new category: Cybersecurity Maturity Intelligence. This is the practice of measuring security posture at the control level, in a way that is simultaneously:

The framework achieves this through three design principles that distinguish it from every conventional alternative:
Specificity over abstraction: 270 specific, auditable controls replacing broad categories that obscure operational reality.
Regulatory defensibility: Control-level regulatory mapping at article granularity, enabling organizations to respond to any regulatory inquiry with pre-assembled, structured evidence.
Financial quantification: Every finding translates into a cyber debt estimate and regulatory fine exposure figure that executives can directly incorporate into investment decisions.
For the first time, an organization can answer three questions simultaneously from a single assessment: Are we secure? Are we compliant? Are we investing correctly? NS-CMMF v1.0 is the instrument that makes all three questions answerable, with evidence, precision, and financial clarity.
The Nucleus Systems Difference: Built by Practitioners, for Practitioners
NS-CMMF v1.0 was not built as a theoretical exercise. It was built by a team of cybersecurity practitioners, regulatory compliance specialists, and enterprise risk professionals who have collectively spent decades conducting assessments, managing incidents, advising boards, and responding to regulatory investigations across multiple continents and industries.
This experience is embedded in every design decision: the weighting of domain criticality reflects empirical observation of where organizations actually fail under regulatory scrutiny; the evidence tier system reflects the lived reality of what data room evidence, audit committee presentations, and regulatory investigations actually require; and the financial quantification model reflects the deal language that investment committees and boards actually use to make decisions.
Nucleus Systems is not introducing another framework. We are defining a new operating standard for measuring cybersecurity maturity, one that is measurable, defensible, and built for the realities of the AI-driven, globally regulated enterprise of 2026 and beyond.