Reframing Critical Infrastructure Risk in the Age of Cyberwar: Water, Energy, Code, and the New Frontline of Systemic Risk
Critical infrastructure is undergoing a profound transformation. Systems once protected by physical barriers and geographic isolation are now digitally driven, interconnected, and exposed to a borderless threat landscape. In this environment, disruption no longer requires destruction. It requires access, persistence, and precise timing, shifting systemic risk into software, networks, and operational technology environments that often remain invisible until impact is felt. In this thought leadership piece, Godfrey Kutumela explores how cyber threats have evolved from disruption to strategic positioning, and what a credible response requires. From strengthening OT security fundamentals and integrating governance across IT and OT, to adopting AI-driven monitoring and resilience testing, the article provides a practical perspective on securing critical systems in an era where apparent normalcy is no longer a reliable indicator of security.
4/30/202616 min read
There was a time when protecting critical infrastructure was primarily a physical undertaking consisting of perimeter fences, access badges, redundant mechanical systems, and geography itself formed the defensive line. Energy plants were secured by distance, and water facilities were protected by obscurity. The thinking was intuitive: if an adversary cannot physically reach a system, the system is safe. That logic no longer holds. And it has not held for some time.
The operational core of modern critical infrastructure has migrated into software, networks, industrial control systems, and increasingly, AI-assisted decision layers. What was once mechanical is now digital. What was once isolated by design is now interconnected by necessity. What was once protected by geography is now exposed to a threat environment that recognizes no borders, no business hours, and no distinction between peacetime and conflict.
This is not a cause for alarm in isolation. It is a cause for recalibration. The same digital transformation that has made infrastructure smarter, more efficient, and more responsive has also created a new category of vulnerability, one that is structural, often invisible, and continuously evolving, and understanding that vulnerability is the first step toward addressing it effectively.
“Infrastructure no longer needs to be physically destroyed to be neutralized. It only needs to be accessed, understood, and manipulated at the time of need for the adversary to exact maximum harm.”
The question this article explores is not whether critical infrastructure faces cyber threats, which is now beyond reasonable dispute. The more useful question is: what does the current threat environment actually look like, and what does a credible response to it require?
I. The Invisible Dependency: Digitization as Structural Transformation
Digital systems do not merely support modern critical infrastructure; in most sectors, they are fundamentally dependent on it for safe and continuous operation. Industrial Control Systems (ICS), SCADA environments, IoT sensor networks, cloud-based analytics platforms, and remote management tools now form the operational backbone of energy, water, transport, and communications infrastructure globally.
This dependency was not accidental. It reflects deliberate decisions to optimize efficiency, reduce operating costs, enable remote management, and integrate real-time data into operational decision-making. These are legitimate and valuable outcomes. But they have introduced a set of structural characteristics that change the risk profile of these systems in ways that older governance and security frameworks were not designed to address.
Consider what digitization actually means for an infrastructure operator:
• Operational continuity is now a function of digital integrity. A failure in software, identity systems, or network segmentation can halt operations without any physical damage to the facility itself.
• Automation reduces manual intervention but also manual detection. Systems designed for efficiency often remove the human oversight layer that might otherwise notice anomalous behavior.
• Interconnectivity creates efficiency and fragility simultaneously. Systems optimized for integration across functions are also, by that same design, conducive to lateral movement once an adversary has gained initial access.
• Remote access expands the attack surface beyond physical geography. Maintenance, monitoring, and control now frequently rely on external network connectivity, introducing dependencies that extend well beyond the facility perimeter.
• Legacy systems coexist with modern layers. Many infrastructure environments operate hybrid architectures in which older, unpatched systems are linked to newer digital platforms, creating vulnerabilities at the interface between generations of technology.
None of these characteristics represents a failure of design intent. They are the natural consequences of a technological transition that has delivered genuine operational benefits. The challenge is that the security architecture has not always kept pace with the transformation.
The result is a paradox at the heart of this discussion: the more sophisticated and digitally integrated the infrastructure becomes, the more exposed it may be to threats that physical security measures alone cannot address. Recognizing this paradox is not pessimistic. It is the starting point for an honest and productive security conversation.
II. A Shift in Threat Doctrine: From Disruption to Strategic Positioning
The past five years have marked a notable shift in how cyber operations relate to critical infrastructure. The objective is no longer primarily disruption in the traditional sense, a visible, immediate event that announces itself. Increasingly, analysts and security researchers have observed a pattern better described as strategic positioning: the sustained, patient accumulation of access within target environments, often held in reserve for activation under conditions of the adversary’s choosing.
Several case studies have become reference points for understanding how this pattern has evolved in practice.
Colonial Pipeline (United States, 2021)
A ransomware attack on Colonial Pipeline, one of the largest fuel distribution systems in the eastern United States, demonstrated how a single compromised credential could cascade into national-level operational disruption. The pipeline was shut down as a precautionary measure, triggering fuel shortages, public concern, and significant economic impact across multiple states. The vulnerability exploited was not exotic; it involved a VPN account with a reused password and no multi-factor authentication. The lesson was not that sophisticated attacks are inevitable. It was that foundational security gaps in critical systems carry outsized consequences.
Oldsmar Water Treatment Facility (United States, 2021)
An incident at a water treatment facility in Oldsmar, Florida, illustrated a different dimension of the threat. An attacker gained remote access to the facility’s control systems and briefly altered the sodium hydroxide concentration in the water supply to potentially harmful levels. Plant operators detected the change and reversed it quickly. No harm resulted. But the incident raised an important question that has since informed global water-sector security discussions: what would the outcome have been if the change had been less visible or if detection had been delayed?
Ukraine (2022–2024): Cyber as an Integrated Component of Conflict
The conflict in Ukraine provided the most sustained and studied example of cyber operations being integrated into a broader military and strategic campaign. Energy infrastructure, telecommunications, and logistics systems faced coordinated cyber pressure that, in many instances, appeared calibrated to complement physical operations. Analysts have characterized this integration as evidence that cyber capabilities have matured into a genuine force multiplier within state conflict doctrine, not a standalone tool, but one element of a converged strategy.
Supply Chain Vulnerabilities: The MOVEit Pattern
The 2023 exploitation of the MOVEit file transfer software vulnerability illustrated a structural feature of modern cyber risk: a single vulnerability in a widely deployed component can affect hundreds of organizations simultaneously, across sectors and geographies. This pattern, sometimes described as supply chain exploitation, is particularly relevant for infrastructure operators who rely on commercial software platforms, managed service providers, and third-party remote access tools. The organization’s own systems do not bound the attack surface.
Taken together, these cases suggest an emerging operational doctrine among sophisticated threat actors:
“Do not destroy immediately. Persist. Learn. Position. Act when it matters most.”
The security implications of this doctrine are significant. A threat that is designed to remain below the detection threshold, prefers persistence over visibility, and activates only under strategically chosen conditions is qualitatively different from the disruption-focused attacks that earlier security frameworks were designed to address. It requires a different kind of vigilance.
III. The Gulf Region Context: Digitization, Ambition, and Exposure Profile
The Gulf Cooperation Council (GCC) region occupies a particular position in the global critical infrastructure security landscape. Over the past decade, GCC member states have undertaken some of the most ambitious digital transformation programs anywhere in the world, including smart cities, automated utilities, AI-driven public services, digitized port and logistics operations, and fully integrated government service platforms.
These programmes have delivered genuine value. They have improved service delivery, reduced operational costs, attracted foreign investment, and positioned the region’s economies for the post-hydrocarbon transition that most governments have identified as a strategic priority.
At the same time, this rapid and ambitious digitization has created an exposure profile with characteristics worth understanding clearly.
3.1 The Regional Risk Picture
Industry data and regional security assessments suggest several relevant patterns. However, it is worth noting that the level of public disclosure around specific incidents varies considerably, and the picture is necessarily incomplete from open sources alone.
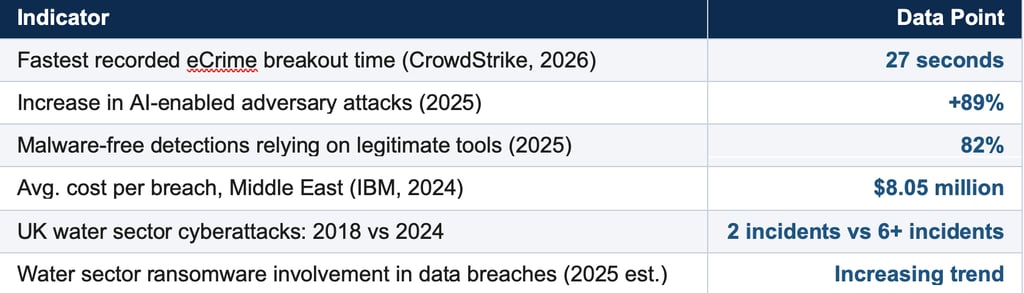
REGIONAL SECURITY INDICATORS
• Average cost per cybersecurity breach in the Middle East: ~$8.05M (IBM, 2024) — nearly double the global average
• CISA and NCSC advisories have explicitly identified GCC energy and water sectors as targets of interest for state-linked actors
• GCC Operational Technology Summit 2025 identified “building a resilient OT environment” as the region’s primary infrastructure security priority
• CSIS analysis has flagged Iran’s shift from episodic to sustained cyber posture, targeting energy, water, and transport sectors
• Multiple GCC telecommunications operators have experienced breach activity attributed by regional analysts to state-linked threat actors
The $8.05 million average cost per breach in the Middle East, nearly double the global figure of $4.45 million, reflects both the concentration of high-value infrastructure assets and the operational complexity of responding to incidents in highly integrated industrial environments. OT environments are not like enterprise IT systems: you cannot simply take a SCADA control system offline for an emergency patch while a desalination plant is running at full capacity.
It is also worth noting what public data does not fully capture. Much critical infrastructure security activity, both incidents and defensive responses, occurs without public disclosure. Security professionals working in the region consistently note that the observable incident record represents only a portion of actual activity. This does not mean the situation is dire; it means that assessments based purely on confirmed public incidents may understate the operational reality.
3.2 The Specific Characteristics of Gulf Infrastructure Risk
Several features of GCC infrastructure create a distinct exposure profile that merits specific consideration rather than generic application of global threat models.
• Centralized control architectures. Gulf infrastructure systems, particularly in utilities and energy, often operate with highly centralized management models that offer significant operational advantages but may also concentrate risk at critical control points.
• Continuous uptime requirements. Energy and water systems in the Gulf operate with very limited tolerance for outages. The operational pressure to maintain continuity can, in some contexts, create tension with the security practice of taking systems offline for patching or testing.
• Rapid adoption trajectories. The pace of digital transformation in the region has, in several cases, outpaced the development of the security governance frameworks needed to manage the resulting risk. This is not unique to the Gulf; it is a pattern observed in ambitious digital transformation programmes globally.
• Geopolitical complexity. The region’s geopolitical environment, characterized by a mix of state, proxy, and non-state actors with varying capabilities and motivations, means that the threat landscape is both active and multidimensional.
IV. Water: The Infrastructure That Cannot Fail
In the Gulf, the relationship between water and security is existential in a way that is not true of most other regions. The Arabian Peninsula receives among the lowest average annual rainfall of any inhabited region on earth. It depends on desalination technology for the overwhelming majority of its potable water supply. These facilities are not simply utilities. They are the physical precondition for population-scale life.
“Water desalination in the Gulf is not just infrastructure. It is the answer to the question: how do tens of millions of people survive in one of the world’s driest environments?”
This dependency creates a security consideration of a qualitatively different order from most infrastructure sectors. When analysts and policymakers assess the consequences of a major cyber incident at a power plant, they consider economic disruption, social inconvenience, and operational recovery timelines. When they assess a major incident at a desalination facility or distribution network in the Gulf, the timeline for consequence becomes considerably shorter and the margin for error considerably narrower.
4.1 The Operational Security Profile of Desalination Infrastructure
Modern large-scale desalination facilities, whether reverse osmosis or multi-stage flash distillation, are highly automated, continuously operating systems. They depend on digital control systems to manage chemical dosing, pressure regulation, flow management, and quality monitoring across complex, interdependent processes.
Security researchers and ICS specialists have, over many years, documented a range of vulnerabilities across water treatment and distribution systems globally. The specific conditions of Gulf desalination infrastructure add several contextual factors:
• The concentration of major desalination capacity at a relatively small number of large facilities creates systemic dependencies, where a small number of installations supply large proportions of regional water demand.
• These facilities are digitally controlled and typically managed with some degree of remote monitoring capability, which, while operationally valuable, extends the potential attack surface.
• The consequences of chemical process manipulation in water treatment, as illustrated, in a different context, by the 2021 Oldsmar incident, include scenarios that carry direct public health implications.
• The intersection of water infrastructure with broader energy and telecommunications systems means that cascading effects across sectors are theoretically possible under certain compromise scenarios.
It is important to state clearly what this analysis does not claim. There is no publicly confirmed evidence of a successful major cyberattack on Gulf desalination infrastructure at the time of writing. Security agencies and facility operators in the region have invested significantly in protection measures, and the absence of major confirmed incidents is itself a meaningful data point.
What security professionals and analysts observe is consistent evidence of reconnaissance, probing, and mapping of OT environments across the energy and water sectors, suggesting sustained interest by threat actors in understanding these systems. Whether and how that interest translates into active operations is a matter of ongoing intelligence assessment rather than confirmed public record.
4.2 The Multi-Domain Risk Dimension
A feature of the current threat environment that has drawn increasing attention from critical infrastructure security specialists is the convergence of cyber risks with physical and informational threats. Facilities that manage essential services face a security environment that may involve not just digital intrusion, but combinations of approaches that are harder to defend against precisely because they do not fit within a single security domain.
This convergence, where cyber, physical, and informational threats may be coordinated rather than sequential, represents a relatively recent development in security thinking. It has influenced how leading organizations approach infrastructure protection, moving from siloed IT and physical security functions toward integrated security architectures that treat these domains as interdependent.
V. The Classification and Governance Opportunity
One of the most consequential questions in critical infrastructure security is definitional: which systems are formally classified as critical, and what governance obligations does that classification create?
The concept of Critical Information Infrastructure (CII), the digital systems whose disruption would have severe consequences for public services, economic stability, or national security, has been formalized in varying degrees across different jurisdictions. Where these frameworks are well-developed and consistently applied, they tend to drive materially better security outcomes by creating clear obligations, enabling coordinated response, and establishing standards that operators must meet.
The opportunity lies in closing the gap between the pace of infrastructure digitization and the development of the governance frameworks that should accompany it. Several areas are particularly relevant:
• Classification consistency. As infrastructure systems digitize, ensuring that their digital control layers are assessed and classified under CII frameworks, not just their physical components, is an important step toward coherent governance.
• IT and OT governance integration. Traditional information security governance was designed around enterprise IT environments. Applying it directly to OT environments, which operate under different constraints, use different protocols, and carry different risk profiles, requires adaptation rather than direct transfer.
• Cross-sector coordination. Modern infrastructure is interconnected. Water systems depend on power. Power systems depend on telecommunications. Governance frameworks that treat these sectors in isolation miss the systemic dimension of the risk they are intended to address.
• Regional coordination mechanisms. In a region where infrastructure is geographically proximate and economically interdependent, cross-border coordination on threat intelligence, incident response, and shared security standards offers significant potential value.
None of these represent new ideas. They appear consistently in international frameworks from the NIST Cybersecurity Framework to the EU NIS2 Directive to CISA’s Critical Infrastructure Security guidelines. The question is less about what needs to be done than about the pace and rigor with which it is pursued.
VI. Dubai as a Reference Model: What Institutional Commitment Looks Like
Within the Gulf region, Dubai’s approach to cyber resilience is worth examining as an example of what institutionalized, strategically grounded cybersecurity governance looks like in practice.
Through the Dubai Cyber Security Strategy, implemented by the Dubai Electronic Security Center (DESC), the emirate has developed an integrated approach that treats cybersecurity not as a technical function performed by IT departments, but as a foundational layer of urban and economic infrastructure. The strategy’s design reflects several principles that have proven effective in other leading cyber-mature jurisdictions:
DUBAI CYBER SECURITY STRATEGY — STRUCTURAL ELEMENTS
• Mandatory Information Security Regulations (ISR) across public sector entities
• Centralized threat intelligence sharing and coordinated incident response capability
• Formal identification and governance framework for Critical Information Infrastructure
• Risk assessment integrated as a core operational requirement, not a periodic exercise
• Active engagement with national and international cyber cooperation frameworks
• Security requirements embedded in the digital transformation and smart city agendas
What makes Dubai’s approach notable is not any single element but the coherence of the overall architecture. Governance, standards, operational capability, and inter-agency coordination are treated as parts of a single system rather than independent programmes. The result is a model that other cities and jurisdictions, in the Gulf and beyond, have studied as they develop their own frameworks.
It is worth acknowledging that Dubai’s context, a city-state with a concentrated administrative structure, significant public investment capacity, and a strong political mandate for digital governance, is not universally replicable. But the underlying design principles, treating security as infrastructure, integrating governance with operational practice, and coordinating across sectors rather than within them, are broadly applicable.
VII. Pathways Forward: What a Credible Response Requires
The threat environment described in this article does not call for panic or the treatment of every infrastructure vulnerability as an imminent crisis. What it requires is a clear-eyed, systematic, and sustained commitment to security practices commensurate with the importance of the systems being protected.
The following areas represent the most operationally consequential priorities based on current threat intelligence, industry research, and governance analysis.
7.1 OT-Specific Security Practices as a Baseline
A foundational observation from security practitioners working in industrial environments is that most successful attacks on OT and ICS systems do not exploit novel, sophisticated vulnerabilities. They exploit well-known weaknesses, default credentials, unpatched legacy systems, inadequate network segmentation, and excessive remote access permissions, that have been documented and addressable for years.
This means that a significant proportion of critical infrastructure risk can be addressed through consistent application of established good practice:
• Maintaining accurate, up-to-date asset inventories for all networked components in OT environments
• Implementing network segmentation that isolates control systems from enterprise IT networks and from public internet exposure
• Enforcing multi-factor authentication for all remote access to industrial control systems
• Establishing and regularly testing patch management processes calibrated to the operational constraints of OT environments
• Defining and maintaining manual override and failsafe capabilities that can sustain operations if digital control systems are unavailable
These measures do not eliminate risk. They substantially reduce the attack surface available to adversaries and raise the cost and complexity of successful intrusion. The fact that they remain unevenly implemented across the critical infrastructure sector is one of the more consequential gaps in the current security landscape.
7.2 IT/OT Convergence: Bridging the Governance and Operational Divide
One of the structural challenges in critical infrastructure security is the historical separation between IT and OT functions within organizations. IT security teams understand enterprise networks, cloud environments, and information security governance. OT engineers understand industrial processes, control system protocols, and operational constraints. These are different disciplines with different priorities, and their convergence, while necessary, requires deliberate investment in shared understanding and integrated governance structures.
Leading organizations have addressed this through dedicated OT security functions, IT/OT integration centers, and joint security operations capabilities that bring together expertise from both domains. The transition takes time and investment. But the alternative, securing converged IT/OT environments with frameworks designed for one but not the other, is increasingly untenable given the sophistication of current threats.
7.3 AI: Both the Threat and a Key Component of the Response
Artificial intelligence has changed the calculus of critical infrastructure security in ways that are still being fully understood. On the threat side, AI tools have enabled adversaries to automate reconnaissance, generate more convincing social engineering content, accelerate exploitation timelines, and develop adaptive malware that modifies itself to evade signature-based detection.
On the defensive side, AI and machine learning tools offer capabilities not previously available at scale: anomaly detection across large, complex OT environments, behavioral analysis to identify unusual patterns in control-system traffic, and automated response capabilities that can react to incidents faster than human operators alone can.
The practical implication for infrastructure operators is that AI-enhanced security monitoring is shifting from a leading-edge investment to a baseline expectation, particularly in high-value sectors such as energy and water. The question is not whether to invest in these capabilities, but how to implement them in ways that are integrated with OT environments and operationally sustainable.
7.4 Scenario-Based Planning and Resilience Testing
One of the most consistently recommended practices in critical infrastructure security and one of the most underutilized in practice is regular, realistic testing of resilience under adverse conditions. Tabletop exercises that incorporate loss-of-visibility and loss-of-control scenarios, red team assessments of OT environments, and cross-sector exercises that simulate cascading failures across interdependent systems are all standard tools in the security practitioner’s kit.
The value of these exercises is not primarily the discovery of specific vulnerabilities, though that often happens. It is the development of organizational muscle memory: the ability for operators, security teams, and executives to respond effectively under pressure, with clear decision frameworks and pre-established communication protocols.
CISA’s guidance on water sector security explicitly recommends annual testing and updating of emergency response plans, exercises incorporating degraded electronic communications scenarios, and the maintained ability to operate in manual mode if digital control systems become unavailable. These recommendations apply with equal force to any high-dependency infrastructure environment.
7.5 Regional and International Cooperation
Cyber threats do not respect the borders that define critical infrastructure ownership and governance. A threat actor targeting GCC energy infrastructure may operate from jurisdictions far removed from the region. Vulnerabilities in shared software platforms affect operators across multiple countries simultaneously. The intelligence needed to anticipate and respond to sophisticated state-linked threats requires information sharing that no single organization or government can generate alone.
The GCC’s existing frameworks for regional cooperation and the individual member states’ bilateral relationships with international security partners provide a foundation for this kind of coordination. Deepening and institutionalizing it, particularly in threat intelligence sharing, joint incident response, and shared security standards for critical sectors, represents one of the most valuable investments the region can make in long-term resilience.
VIII. Conclusion: Apparent Normalcy Is Not the Same as Security
The most important conceptual shift this analysis asks of infrastructure operators, policymakers, and security professionals is a simple but consequential one: the absence of a visible incident is not evidence that a system is secure. In the current threat environment, the systems that are most successfully secured and the systems that are most successfully infiltrated may look identical from the outside for extended periods.
This is not a counsel of despair. It is a call for a different kind of vigilance, one that moves from reactive validation (“nothing has failed, therefore we are safe”) toward proactive assurance (“we understand our security posture and have verified it under realistic conditions”).
“The most dangerous condition is not visible failure. It is apparent normalcy under active, patient compromise.”
Critical infrastructure has never been static. It has always evolved in response to new technologies, new operational requirements, and new threats. The current moment requires that evolution to encompass the digital dimension of infrastructure security with the same seriousness, investment, and institutional commitment that the physical dimension has historically received.
The Gulf region’s infrastructure, particularly its water systems, sits at the center of overlapping dynamics: rapid digitization, complex geopolitics, existential dependence on continuous operation, and an evolving threat landscape that is patient, sophisticated, and strategically motivated.
The good news is that the path toward resilience is well-mapped. The practices, governance frameworks, and technical tools required to strengthen critical infrastructure security are substantially understood and available. What they require, above all, is the organizational and political will to prioritize them not as a response to the next crisis, but in anticipation of it.
Because in this operating environment, the question was never whether these systems would be of interest to adversaries. They already are. The only question that meaningful security work can address is what condition those systems are in when that interest becomes action.
KEY SOURCES AND FURTHER READING
• CrowdStrike 2026 Global Threat Report
• IBM Cost of a Data Breach Report 2024
• CISA: Ongoing Cyber Threats to U.S. Water and Wastewater Systems (AA21-287A)
• CISA: Critical ICS Cybersecurity Performance Goals and Objectives
• CSIS: Iran’s Shift from Episodic Cyberattacks to Sustained Campaign Against Critical Infrastructure (April 2026)
• TXOne Networks: Cyber Threats to the Water and Wastewater Sector (2025)
• GEO Geopolitical Intelligence: OT, ICS, and SCADA — Critical Infrastructure Clarity for the GCC (2025)
• GCC Operational Technology Summit 2025 — Building a Resilient OT Environment
• Dubai Electronic Security Center (DESC): Dubai Cyber Security Strategy
• Trend Micro: Exposed and Vulnerable Critical Infrastructure — Water and Energy Industries
• NIST SP 800-82 Rev. 2: Guide to Industrial Control Systems (ICS) Security
• Verizon Data Breach Investigations Report (DBIR) 2025
• The Cradle: Water on the Brink — Gulf Desalination Frontlines (March 2026)